A new ransomware called TeslaCrypt is one of the latest threats for Windows users. As you probably know already, a ransomware is a virus that crypts every personal file present in your computer and asks for a ransom in order to give you back access to them.
Very similar to Cryptowall or Cryptolocker, once in your PC TeslaCrypt will search for every file that might have some value for you: word and excel files as well as pictures are the obvious choices. However, TeslaCrypt doesn’t stop there, it also crypts backup data from video games installed in your computer. TeslaCrypt can actually crypt files from over 40 games including: Call of Duty, Star Craft 2, Diablo, Fallout 3, Minecraft, Half-Life 2, Dragon Age: Origins, Skyrim, WarCraft 3 among others.
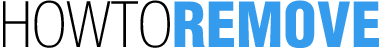
Another important difference between TeslaCrypt and other ransomware is that for the first time, this kind of infection accepts payments from another source than bitcoin, in this case we talk about payments with PayPal My Cash Card. These cards are prepaid cards found in shops in the United States, money can be uploaded to them to be used in a PayPal account. If you pay with a PayPal My Cash, your ransom will be $ 1000, using bitcoin the amount is $ 500.
TeslaCrypt is deployed by malicious websites using a combination of Flash and iframes to infect their visitors. Once infected, it scans every hard drive in your computer to crypt the previously mentioned file types by means of the AES crypt system. Every encrypted file will have the .ecc extension added to their name. Afterwards it will execute a command that will erase every backup and restoration points created by Windows. This is a clever way to stop you from getting back your files from one of these sources.
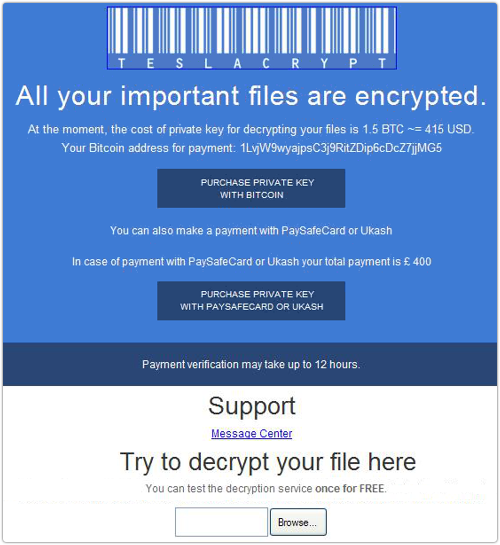
Finally, TeslaCrypt will change your wallpaper to set a picture asking for the ransom, and will create a file called: HELP_TO_DECRYPT_YOUR_FILES.txt in your desktop. A window will appear with explanations about what has happened to you files, and warning you that you have 3 days to pay. This window has special cases where you can verify if your payment has been accepted and to enter the keys to recover your files and a link towards a TOR site where you can recover one file as a test.

How to remove TeslaCrypt ?
Remove TeslaCrypt with MalwareBytes Anti-Malware
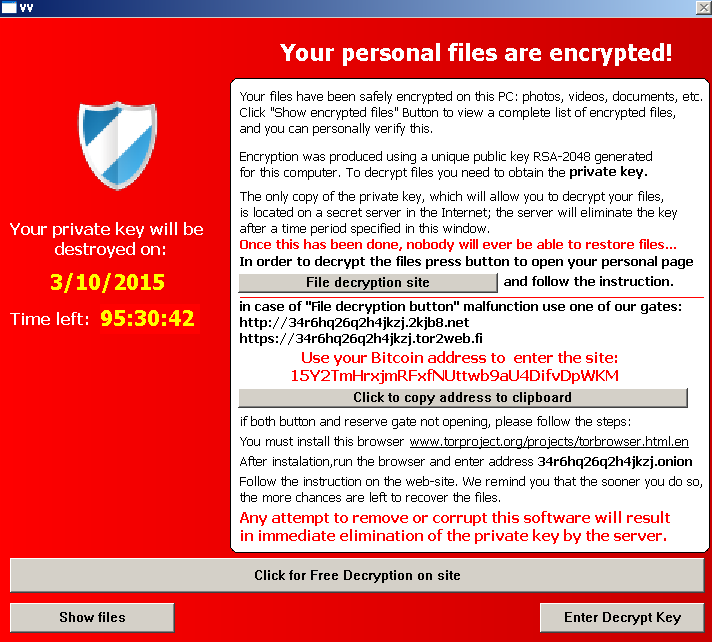
Malwarebytes Anti-Malware is a light-weight anti-malware program that is excellent at removing the latest detections.
- Download Malwarebytes Anti-Malware to your desktop.
Premium Version Free Version (without Real-time protection) - Install MalwareBytes Anti-Malware using the installation wizard.
- Once installed, Malwarebytes Anti-Malware will automatically start and you will see a message stating that you should update the program, and that a scan has never been run on your system. To start a system scan you can click on the Fix Now button.
- If an update is found, you will be prompted to download and install the latest version.
- Malwarebytes Anti-Malware will now start scanning your computer for TeslaCrypt.
- When the scan is complete, make sure that everything is set to Quarantine, and click Apply Actions.
- When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
Remove TeslaCrypt with HitmanPro
HitmanPro is a second opinion scanner designed to rescue computers that have become infected with viruses, spyware, Trojans, rootkits and other malware, despite continuous protection from up-to-date antivirus software.
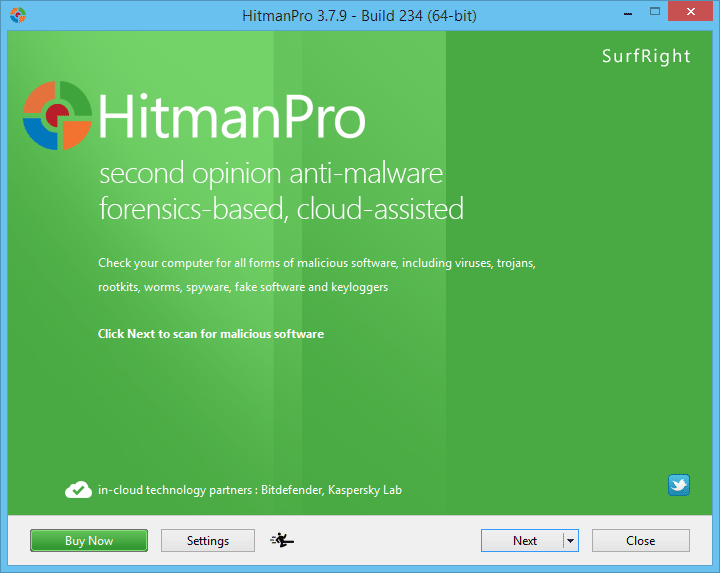
- You can download HitmanPro from the below link:
Download HitmanPro - Double-click on the file named HitmanPro.exe (for 32-bit versions of Windows) or HitmanPro_x64.exe (for 64-bit versions of Windows).
- Click on the Next button, to install HitmanPro on your computer.
- HitmanPro will now begin to scan your computer for TeslaCrypt malicious files.
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the Next button, to remove TeslaCrypt virus.
Click here to go to our support page.